TeamCognito.
HARDWARE HACKING

In general definition it can be described and socially accepted as when an electronic device is made to perform a deviated task that it did not intend to perform initially.
In the late 2018,Bloomberg ran a series of stories reporting that China installed spy chips on motherboards manufactured by U.S.-headquartered Super-micro, a company whose motherboards are used by tech companies like Apple and Amazon in their servers.
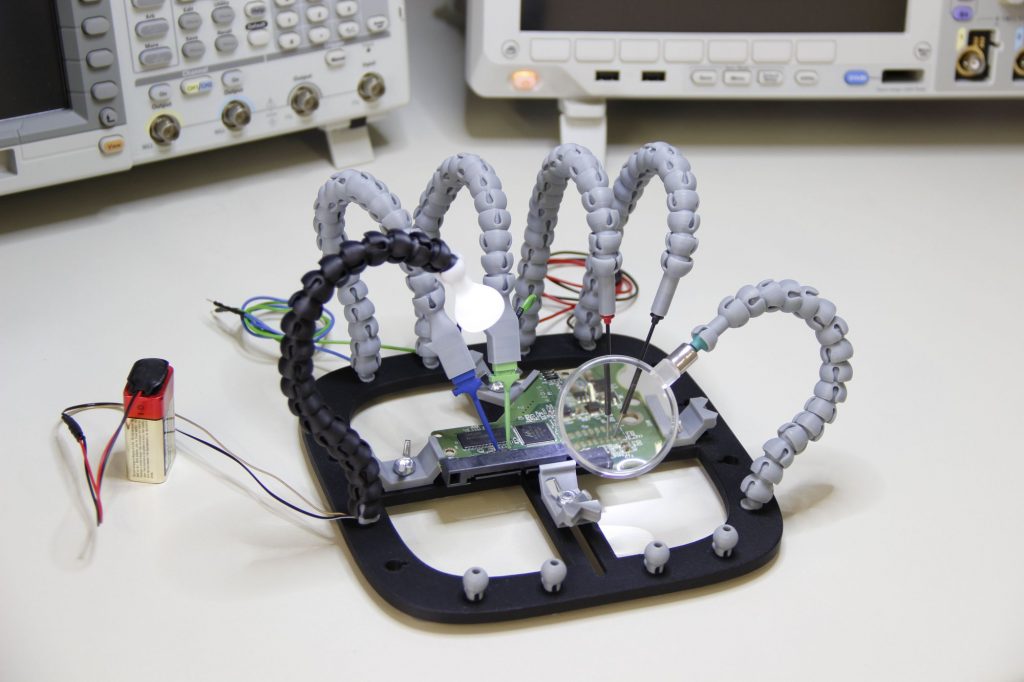
Now as abundant availability of rapid hardware prototyping has come into existence it has been like a boon to the hardware hacking cartels. It can be used for many purposes and of those some of are privacy breach, system spying, system crashing, blackmailing someone for money in exchange of their privacy and for God’s sake many more.
As in one of those paragraphs I have mentioned about a Bloomberg’s reports of China putting in spy chips, so just imaging if it’s true and really did happen, just image of you are right now using one of those computers fitted with those, imaging if they get to know that you are reading this from the spy chip they might have put in your laptop or computer. Where are enormously big companies who succumb to these security breaches and lose billions to the market. Well I would like to put some light over some events that took place some years ago, some pretty big companies suffered enormous lose due to unrecognized money transfers to anonymous bank account across the globe and till the time they found out it was way too late they succumbed to sudden bankruptcy then fell down in the market and some anonymous personality bought their shares from their own money and made the company run for billions, well it’s not a true story it’s what I would to if I had expertise in it. This is one of the ways organizations suffer to hardware hackings.
Back in days when we used to buy those PC game disks and some of them would finish the setup but wouldn’t run, out of those some would eventually end up damaging our own system and we were forced to restore the system erasing all the data and reinstalling the windows. So, in this context this does also can contribute to hardware hacking under the condition that the problem in the disc is purposely put to harm the system of the beholder.
To staying safe from breaches like these, governments across the globe have joined hands and procurement of the desired products aTer certain evaluations and only aTer they meet certain standards was made mandatory.